1 # available on the official FreeBSD ports tree
3 From 2017-08, ndproxy is made available from the official FreeBSD ports tree: [ndproxy port at FreeBSD](https://www.freshports.org/net/ndproxy/)
5 This way, you can get precompiled packages for many hardware targets, or install it from the sources, while maintaining dependencies. The port is based on this GitHub source repository content.
9 Kernel module for FreeBSD that implements IPv6 Neighbor Discovery proxying over Ethernet-like access networks
11 With this module, your uplink provider continues to see you as a flat network, but you can subnet your IPv6 prefix and route packets to your preferred gateway (a Cisco router for instance), that may split your network into several subnets. To achieve this goal, your FreeBSD router will redirect packets coming from your uplink provider router to your gateway. You simply need to connect one of your FreeBSD host interfaces to the layer 2 that interconnects your provider and your gateway, and disable MLD snooping on the interconnection switch.
13 Tested with success on FreeBSD 10.x, FreeBSD 11.x, FreeBSD 12.x and CURRENT (FreeBSD 13)
15 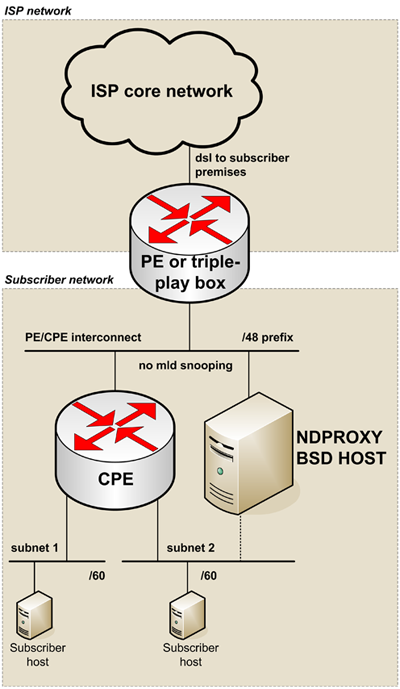
18 NDPROXY(4) FreeBSD Kernel Interfaces Manual NDPROXY(4)
21 ndproxy -- Neighbor Discovery Proxy
24 ndproxy is a kernel module that implements IPv6 Neighbor Discovery proxy-
25 ing over Ethernet-like access networks, with many options to handle sev-
28 ndproxy replies to a neighbor solicitation with a specific neighbor ad-
29 vertisement, in order to let the PE uplink router send further packets to
30 a CPE downlink router, that may or may not be the same node that run nd-
33 The hook-based pfil(9) framework is used to let ndproxy be invoked for
34 every IPv6 incoming packet, in order to specifically handle and filter
35 neighbor solicitations and reply with appropriate neighbor advertise-
38 ND (Neighbor Discovery) packets are mainly targeted at solicited-node
39 multicast addresses, but ndproxy has no information about the hosts to
40 proxy, then it can not join the corresponding groups. Thus, the interface
41 on which ndproxy listen to solicitations must be put into permanently
42 promiscuous mode: add "promisc" to the ifconfig_<interface> variable in
45 For the same reason, MLD snooping must be disabled on the switches that
46 share the PE/CPE interconnect (the layer-2 link the listening interface
47 is attached to). Note that MLD snooping must not be disabled entirely on
48 each switch, but only on the corresponding vlan.
50 The interface on which ndproxy listen to solicitations only need to be
51 assigned a link-local address. No information about the delegated prefix
52 and no global address are needed on this interface. It is sufficient to
53 add "inet6 -ifdisabled -accept_rtadv auto_linklocal" to the ifconfig_<in-
54 terface>_ipv6 variable in rc.conf(5).
57 The target address to proxy must be given when using the ndp(8) command-
58 line tool with the proxy option. On the contrary, ndproxy does not rely
59 on a list of target addresses to proxy. Thus, RFC-4941 temporary ad-
60 dresses can be proxyfied. For security reasons, many operating systems
61 use a temporary address when establishing outbound connections.
63 When using ndp(8) command-line tool with the proxy option, the proxyfied
64 packets are redirected to the node that run ndp. With ndproxy, the host
65 that run ndp can be used only to redirect packets to another IPv6 inter-
66 nal router, for instance a dedicated router with hardware support of IPv6
70 Connecting a flat IPv6 network to the Internet is easily done with the
71 RFC-4861 ND protocol. But connecting a subnetted IPv6 prefix is more com-
72 plicated, depending on the ISP network design choices. ndproxy can help
73 subscribers to achieve this goal.
75 Here are some protocols or mechanisms the ISP need to support, when the
76 delegated prefix must be subnetted and assigned to multiple links within
77 the subscriber's network. For instance, the ISP could learn routes from
78 the subscriber router using an IGP routing protocol, but the ISP and the
79 subscriber must agree with a common routing protocol. The ISP could also
80 feed the PE with a static route to the CPE router, but the ISP must be
81 informed about the subscriber router address. Finally, the ISP could use
82 the RFC-3633 IPv6 Prefix Options with DHCPv6 to delegate the prefix from
83 its PE router to a requesting subscriber's router: in such a case, the
84 ISP must support the DHCPv6 option.
86 ndproxy has been written for subscribers to ISP that do not support any
87 of those mechanisms or protocols, thus not being able to natively subnet
88 their IPv6 delegated prefix.
91 Here is a generic network design using ndproxy to solve such situations:
92 ______________________ \
94 | ISP core network | \
95 \__________ ___________/ |
97 | dsl to subscriber premises |
99 +---+---------------------+ /
100 | PE or triple-play box | /
101 +-----------+-------------+
103 PE/CPE interconnect | /48 prefix \
104 --+---------+---------+-- \
105 | no mld snooping | \
107 +----+--------+ +----+-----+ |
108 | CPE | | ndproxy | |
109 | IPv6 router | | BSD host | |
110 +----+---+----+ +----------+ |
111 subnet1 | | subnet2 | Subscriber
112 ----+-----+- -+-----+------ | network
114 +---+------+ +----+-----+ |
115 |Subscriber| |Subscriber| /
117 +----------+ +----------+ /
119 Note that many other use-cases can be handled with ndproxy: the BSD host
120 and the CPE router can be the same node, the delegated-prefix length can
121 be /64, the PE router can have several interfaces on the ISP/Subscriber
122 layer-2 boundary, there can be multiple PE routers, etc.
125 Even if the IESG and the IAB first recommended the allocations of /48
126 prefixes in the general case, for the boundary between the public and the
127 private topology (see RFC-3177), and that some Regional Internet Reg-
128 istries (APNIC, ARIN and RIPE) have subsequently revised the end site as-
129 signment policy to encourage the assignment of /56 blocks to end sites,
130 and that RFC-6177 finally recommended giving home sites significantly
131 more than a single /64, in order for home sites to be given multiple sub-
132 nets, some ISP currently only delegate /64 prefixes.
134 In such a case, the subscriber should subnet a RFC-4193 Unique Local IPv6
135 Unicast Addresses prefix to the internal subnetworks, for internal-to-in-
136 ternal communications. The /64 global prefix should be routed to the only
137 internal subnet in which RFC-4941 temporary addresses are used by hosts
138 when establishing outbound connections. Static routes on the CPE router
139 should be set to let hosts on other internal subnets be able to communi-
140 cate with the Internet. Using temporary addresses for outbound connec-
141 tions to the Internet must be disabled on hosts on those other internal
144 IPv6 EXTENSION HEADERS
145 For security reasons, ndproxy explicitely rejects neighbor solicitation
146 packets containing any extension header. Such a packet is mainly unat-
151 According to RFC-6980, IPv6 fragmentation header is forbid-
152 den in all neighbor discovery messages.
156 commonly used for jumbograms or for MLD. Should not involve
157 neighbor solicitation packets.
159 Destination mobility headers:
161 commonly used for mobility, ndproxy does not support these
166 commonly used for mobility or source routing, ndproxy does
167 not support these headers.
171 securing the neighbor discovery process is not done with
172 IPsec but with the SEcure Neighbor Discovery protocol
173 (RFC-3971). ndproxy can not support RFC-3971, since proxi-
174 fying ND packets is some kind of a spoofing process.
177 Some neigbhor solicitations sent on the PE/CPE interconnect must not be
180 1. solicitations sent by other nodes than the PE;
182 2. solicitations sent by the PE to reach any on-link address (the ad-
183 dress filled in the target address option) owned by nodes attached
184 to the PE/CPE interconnect, for instance to reach the CPE, the nd-
185 proxy host or other hosts attached to this layer-2 interconnect.
187 The target addresses filled in those solicitations that ndproxy must ig-
188 nore have to be declared via sysctl (net.inet6.ndproxyconf_excep-
189 tion_ipv6_addresses). This list must contain the link-local and global-
190 scoped unicast and anycast addresses of the CPE, of the ndproxy host and
191 of any other host than the PE attached to the PE/CPE interconnect.
193 Failing to maintain this list correctly could lead to badly redirect some
194 packets to the CPE, but with a simple network design, this list can be
197 UPLINK ROUTER ADDRESSES
198 ndproxy only handles packets originating from one of the PE addresses.
199 During its address resolution process, different source addresses can be
200 choosen by the PE, depending on the packet that triggered the process or
201 depending on other external constraints.
203 Here are some cases when it can occur:
205 1. The PE may have multiple interfaces;
207 2. There may be multiple PE;
209 3. Many routers choose to use a link-local address when sending neigh-
210 bor solicitations, but when an administrator of such a router, also
211 having a global address assigned on the same link, tries to send
212 packets (echo request, for instance) to an on-link destination
213 global address, the source address of the echo request packet
214 prompting the solicitation may be global-scoped according to the se-
215 lection algorithm described in RFC-6724. Therefore, the source ad-
216 dress of the Neighbor Solicitation packet should also be selected in
217 the same global scope, according to RFC-4861;
219 4. When the uplink router does not yet know its own address, it must
220 use the unspecified address, according to RFC-4861.
222 So, it can not be assumed that an uplink router will always use the same
223 IPv6 address to send neighbor solicitations. Each assigned address that
224 can be used as a source address by the PE on its downlink interface must
225 then be declared to ndproxy via sysctl (net.inet6.ndproxyconf_up-
226 link_ipv6_addresses).
228 ndproxy will only handle packets that come from one of these addresses.
230 A special care must be taken about the unsolicited address. It may be
231 used by the PE, then it is part of the list of PE addresses and should
232 therefore be added to the list of PE addresses. Since this address can
233 also be used by other nodes during some initialization steps (for in-
234 stance when hot-swapping an Ethernet board), another node could use this
235 address to send neighbor solicitations that ndproxy should not handle,
236 because they are not sent by the PE. In fact, this is not a problem be-
237 cause the target address option contained in a solicitation from this
238 other node should be in the exception list. So, adding the unsolicited
239 address in the PE addresses list should be safe.
241 Failing to maintain this list correctly could lead the PE not to be able
242 to establish outbound connections to nodes on the PE/CPE interconnect,
243 but if this list contains at least the PE link-local address, IPv6 con-
244 nectivity should be correctly established between the Internet and the
245 internal subscriber's subnets.
248 An IPv6 address can be any valid textual representation according to
249 RFC-4291 and RFC-5952 (this means that transitional textual representa-
250 tion is fully supported). Other representations will trigger an error
251 event. IPv6 address lists must be formated as series of IPv6 adresses
252 separated by semi-colons.
254 The sysctl utility or rc.conf(5) are used to set ndproxy configuration
257 If you have installed ndproxy as a port or as a package, set the follow-
258 ing variables in rc.conf(5) and load the module at boot time by placing
259 the following line in rc.conf(5):
263 On the contrary, if you have NOT installed ndproxy as a port or as a
264 package but as a standalone distribution, place the sysctl entries in
265 sysctl.conf(5) and load the module at boot time by placing the following
266 line in loader.conf(5):
270 net.inet6.ndproxyconf_uplink_interface sysctl entry or
271 ndproxy_uplink_interface rc.conf variable:
273 Name of the interface talking to the broadcast multi-access
274 network connecting the PE and CPE routers.
278 net.inet6.ndproxyconf_downlink_mac_address sysctl entry or
279 ndproxy_downlink_mac_address rc.conf variable:
281 MAC address of the CPE router. Neighbor advertisements sent
282 by ndproxy will be filled with this address in the target
283 link-layer address option. The format of this parameter is
284 the hexadecimal representation made of 6 groups of 2 hexa-
285 decimal numbers separated by colons.
287 Example: "00:0C:29:B6:43:D5".
289 net.inet6.ndproxyconf_exception_ipv6_addresses sysctl entry or
290 ndproxy_exception_ipv6_addresses rc.conf variable:
292 Target addresses not to proxy. In a simple network design,
293 this list can be let empty. See section "EXCEPTION AD-
297 "fe80::20d:edff:fe7b:68b7;fe80::222:15ff:fe3b:59a".
299 net.inet6.ndproxyconf_uplink_ipv6_addresses sysctl entry or
300 ndproxy_uplink_ipv6_addresses rc.conf variable:
302 Addresses of the PE. This list should at least contain the
303 PE link-local address. See section "UPLINK ROUTER AD-
307 "fe80::207:cbff:fe4b:2d20;2a01:e35:8aae:bc60::1;::".
309 net.inet6.ndproxycount sysctl entry:
311 Number of advertisements sent.
314 inet6(4), rc.conf(5), loader.conf(5), sysctl.conf(5), sysctl(8),
318 Alexandre Fenyo <alex@fenyo.net> - www.fenyo.net
320 FreeBSD 13.0 May 27, 2017 FreeBSD 13.0